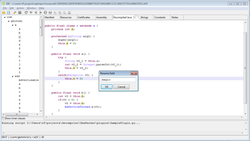
JEB is a disassembler and decompiler software for Android applications[2] and native machine code. It decompiles Dalvik bytecode to Java source code, and x86, ARM, MIPS, RISC-V machine code to C source code. The assembly and source outputs are interactive and can be refactored. Users can also write their own scripts and plugins to extend JEB functionality.
 | |
 | |
| Original author(s) | Nicolas Falliere |
|---|---|
| Developer(s) | PNF Software, Inc. |
| Stable release | 5.19
/ October 29, 2024[1] |
| Written in | Java |
| Operating system | Microsoft Windows, Mac OS X, Linux |
| Platform | Java |
| Type | Reverse engineering |
| License | Proprietary |
| Website | www |
Version 2.2 introduced Android debugging modules for Dalvik and native (Intel, ARM, MIPS) code. Users can "seamlessly debug Dalvik bytecode and native machine code, for all apps [...] including those that do not explicitly allow debugging".[3]
Version 2.3 introduced native code decompilers. The first decompiler that shipped with JEB was a MIPS 32-bit interactive decompiler.
JEB 3 ships with additional decompilers, including Intel x86, Intel x86-64, WebAssembly (wasm), Ethereum (evm), Diem blockchain (diemvm).
JEB 4 was released in 2021. A RISC-V decompiler was added to JEB 4.5. A S7 PLC block decompiler was added to JEB 4.16.
JEB 5 was released in 2023.
History
editJEB is the first Dalvik decompiler to provide interactive output, as reverse-engineers may examine cross-references, insert comments, or rename items, such as classes and methods. Whenever possible, the correspondence between the bytecode and the decompiled Java code is accessible to the user. Although JEB is branded as a decompiler, it also provides a full APK view (manifest, resources, certificates, etc.). An API allows users to customize or automate actions through scripts and plugins, in Python and Java.
The name may be a reference to the well-known security software IDA, as "JEB" = rot1("IDA").
Decompilers
editJEB ships with the following proprietary and open-source decompiler plugins:
- Dalvik bytecode to Java
- Java bytecode to Java
- Intel x86/x86-64 machine code to C
- ARM machine code to C
- MIPS machine code to C
- RISC-V machine code to C
- S7 (MC7) bytecode to C
- WebAssembly bytecode to C
- EVM bytecode (compiled Ethereum smart contracts) to Solidity-like source code
- Diem bytecode[4] (compiled diemvm modules run on the Diem blockchain) to mvir-like (Move IR) source code
Other plugins
editJEB ships with a sizable number of disassemblers and debugger plugins.[5]
JEB allows parsing of any file format, via the addition of native or third-party plugins. Examples include: a PDF parser plugin (proprietary), an XLS document plugin (open-sourced).
See also
editReferences
edit- ^ JEB changelist
- ^ Chell et al. The Mobile Application Hacker's Handbook Page 240-241. 2015
- ^ JEB Product Description page
- ^ GitHub Repository
- ^ Features Matrix